La vulnerabilità riportata per intero così:
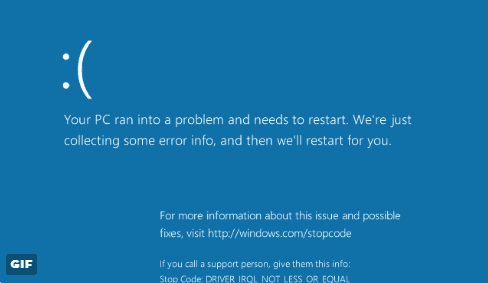
Microsoft Windows fails to properly handle traffic from a malicious server. In particular, Windows fails to properly handle a server response that contains too many bytes following the structure defined in the SMB2 TREE_CONNECT Response structure. By connecting to a malicious SMB server, a vulnerable Windows client system may crash (BSOD) in mrxsmb20.sys. It is not clear at this point whether this vulnerability may be exploitable beyond a denial-of-service attack. We have confirmed the crash with fully-patched Windows 10 and Windows 8.1 client systems.
@PythonResponder quick and dirty gif pic.twitter.com/ccwrrG36rO— Chris Mallz (@vvalien1) 1 febbraio 2017
Fonte: SMB Zero-Day Affects Several Windows Versions, Including Windows 10